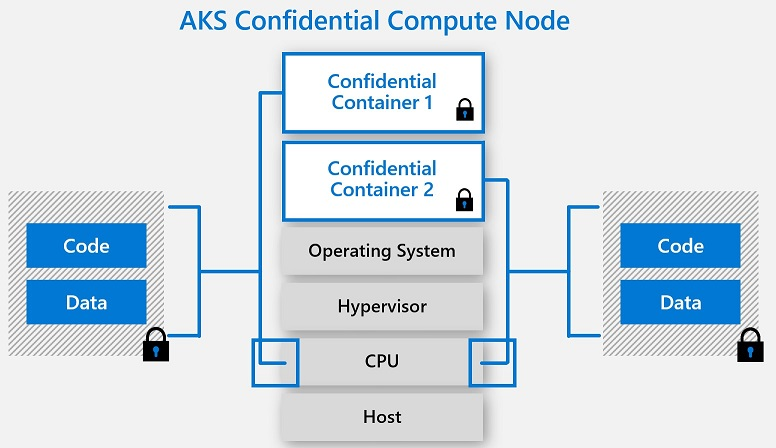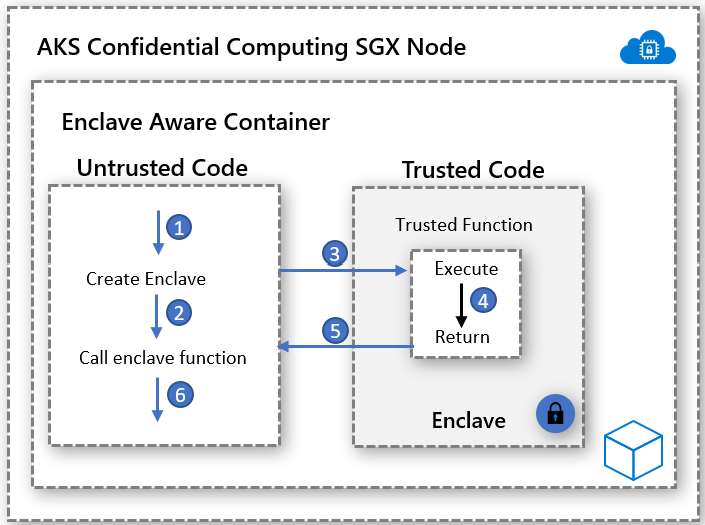
When Kubernetes Encounters Confidential Computing, How Does Alibaba Protect the Data in the Container? - Alibaba Cloud Community
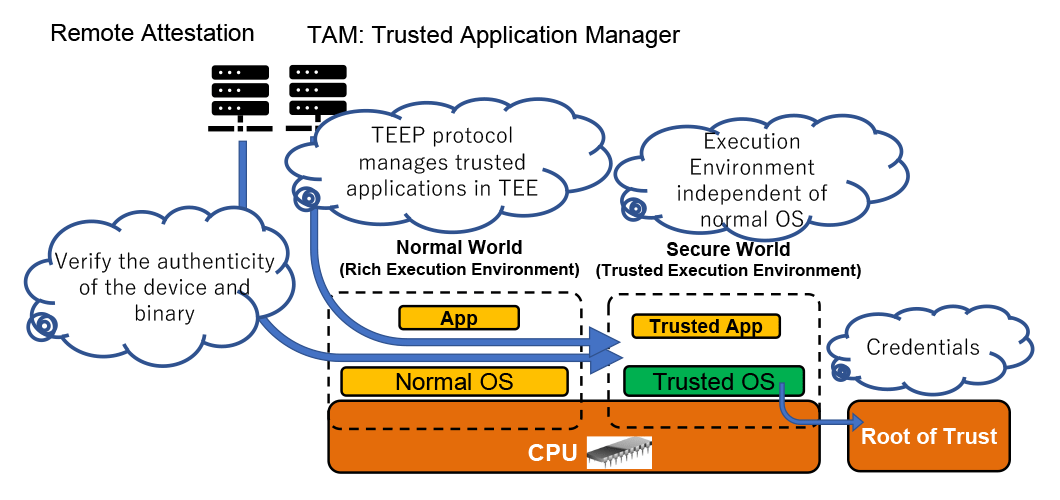
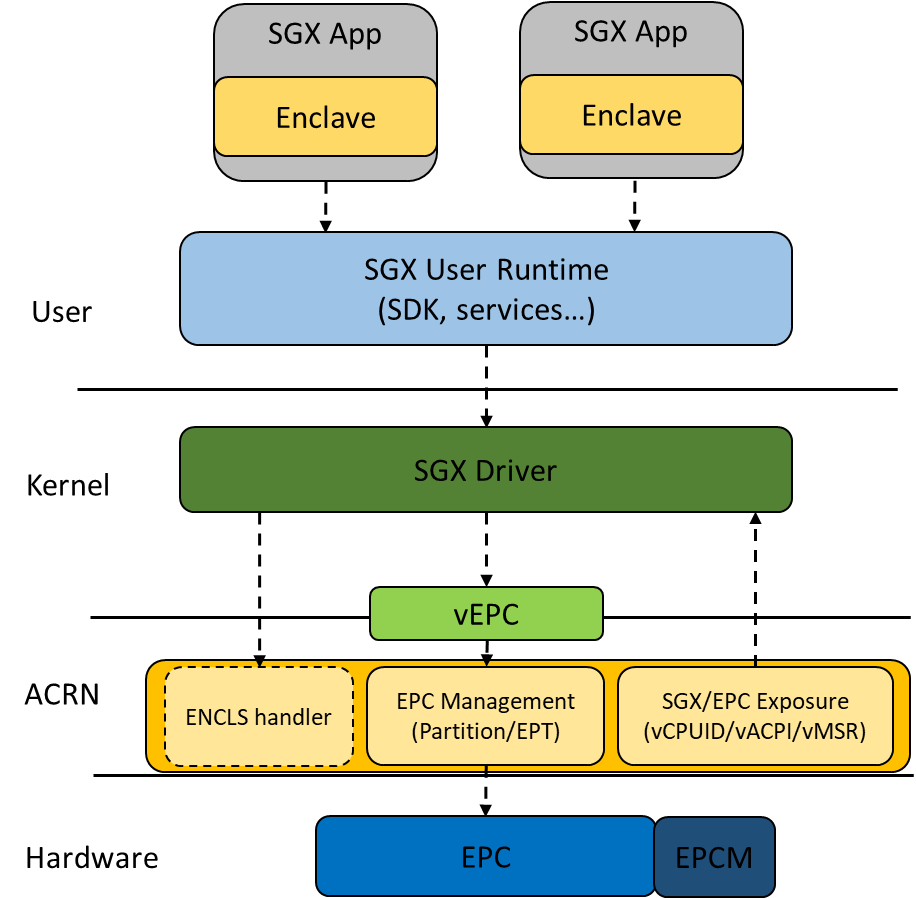
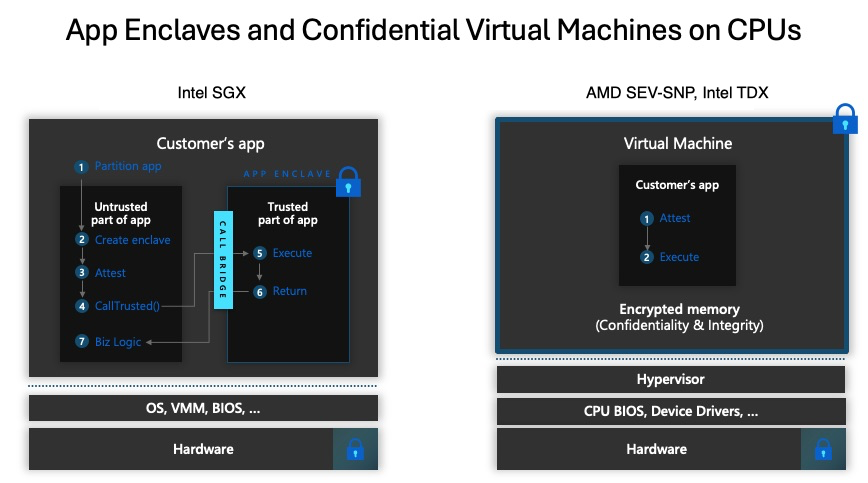
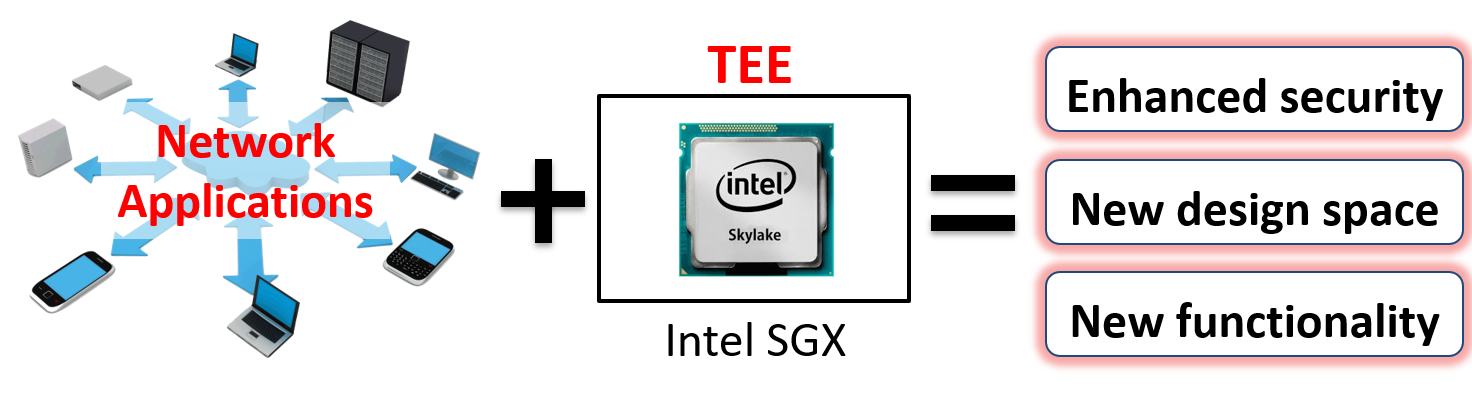
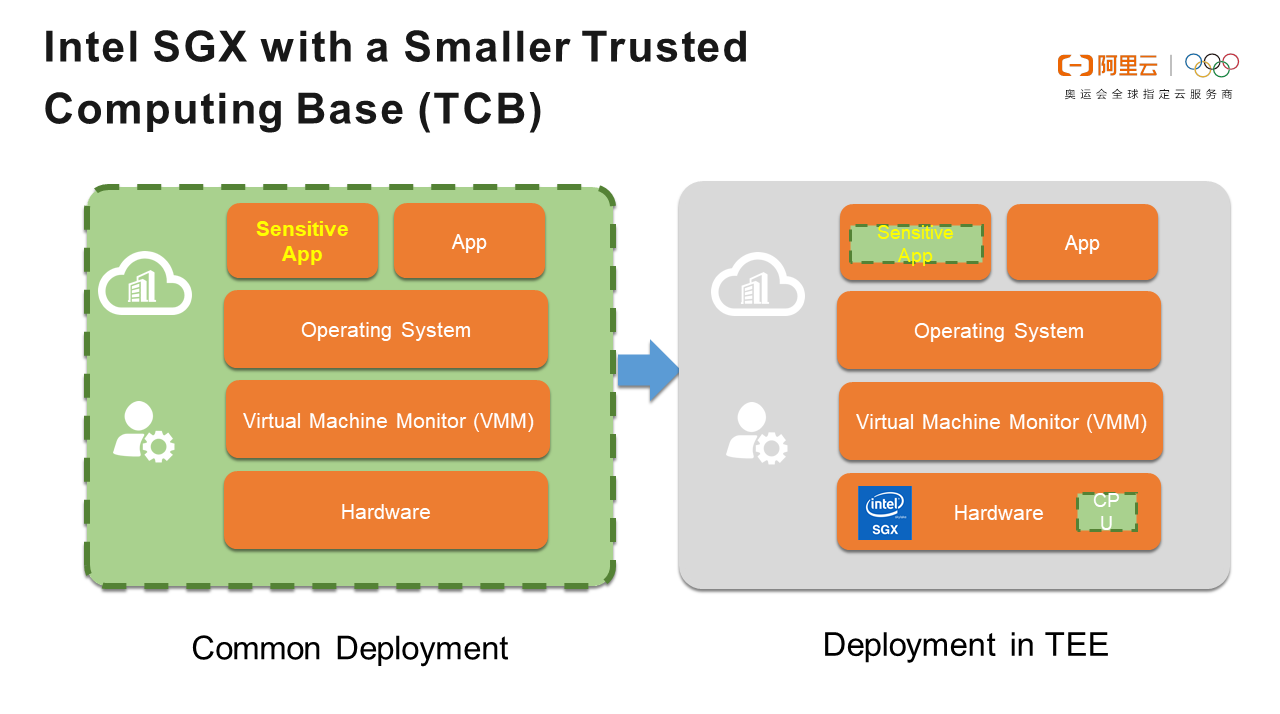
TEE (Trusted Execution Environment) and its supporting technologies | Cryptography Platform Research Team | Cyber Physical Security Research Center - AIST
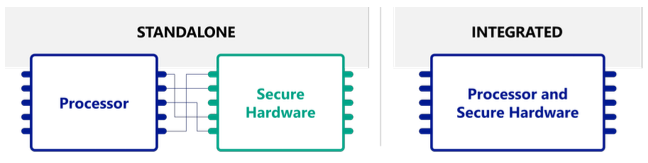
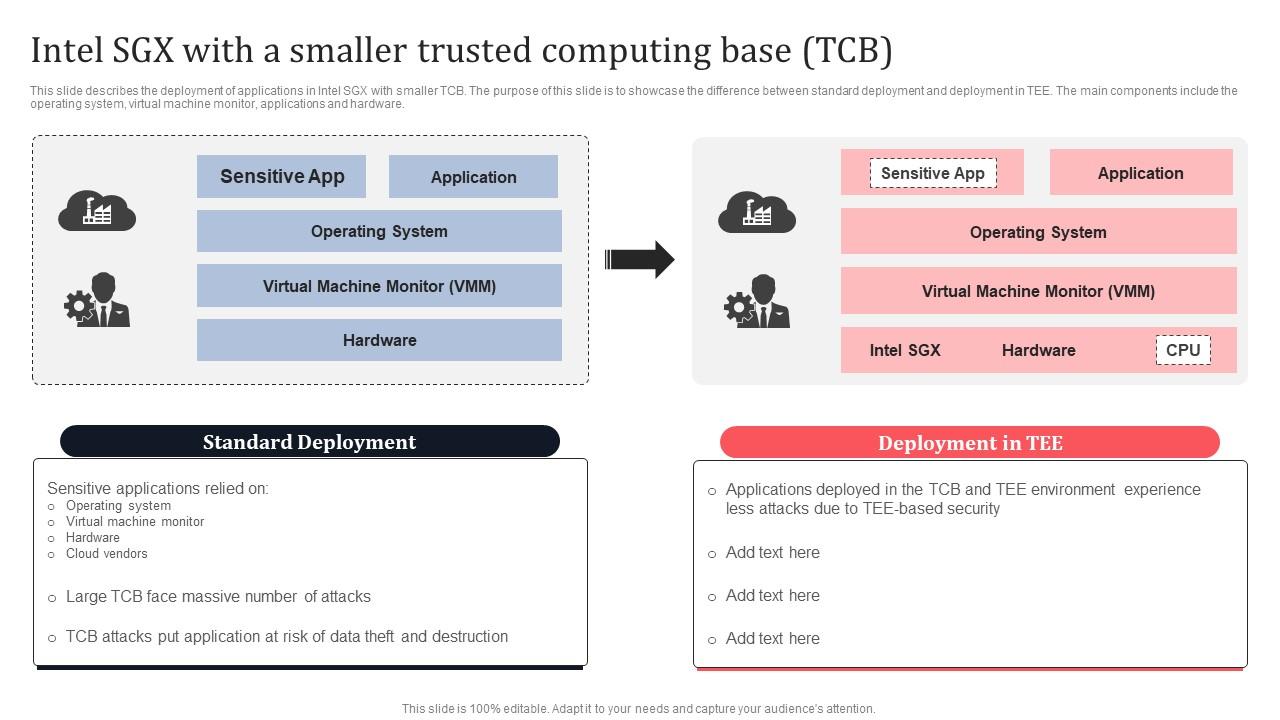
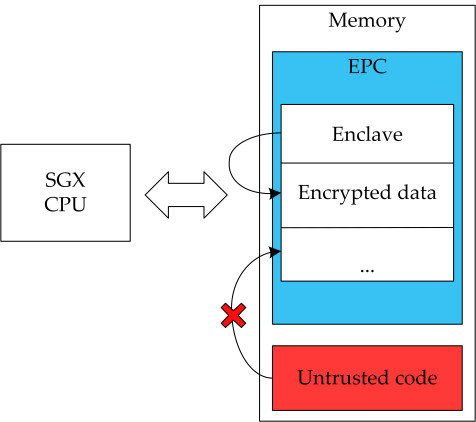
Hardware Solutions To Highly-Adversarial Environments Part 3: Trusted Execution Environment (TEE), SGX, TrustZone and Hardware Security Tokens