Comparison of time taken for various methods of AES key generation and... | Download Scientific Diagram
![PDF] RK-AES: An Improved Version of AES Using a New Key Generation Process with Random Keys | Semantic Scholar PDF] RK-AES: An Improved Version of AES Using a New Key Generation Process with Random Keys | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/02b7e8c5edb6b10d8f31cd08e0b41f6d99ba586e/5-Figure3-1.png)
PDF] RK-AES: An Improved Version of AES Using a New Key Generation Process with Random Keys | Semantic Scholar
Generation of the chaotic keys on the fly for AES encryption system | Graduate School of Management of Technology
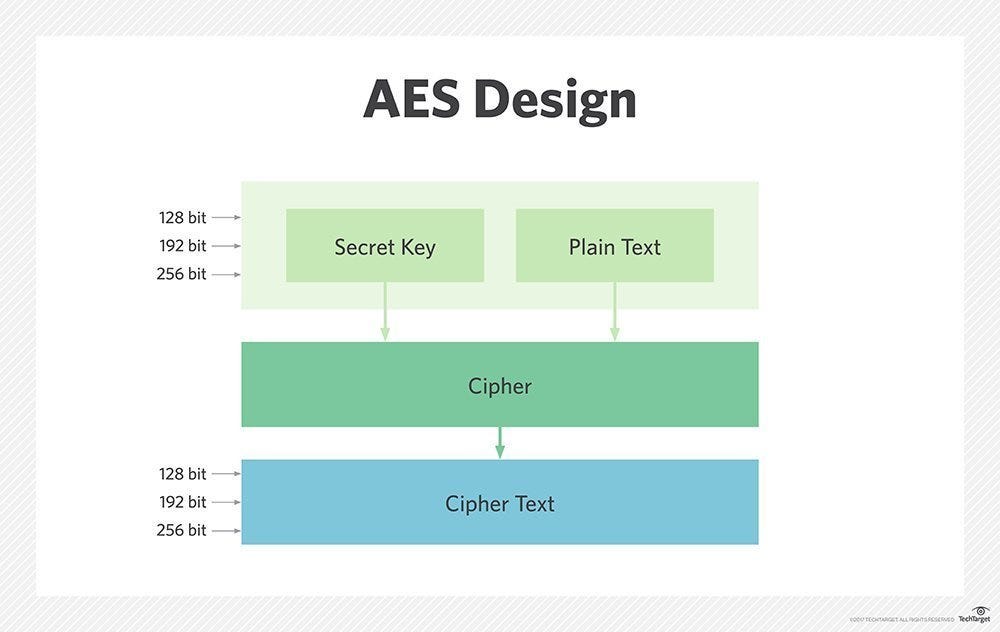
Electronics | Free Full-Text | A Low Area High Speed FPGA Implementation of AES Architecture for Cryptography Application
![cryptanalysis - S-AES RC[i] Generation. Can someone explain how to generate the RC[i]s for these two problems I have? - Cryptography Stack Exchange cryptanalysis - S-AES RC[i] Generation. Can someone explain how to generate the RC[i]s for these two problems I have? - Cryptography Stack Exchange](https://i.stack.imgur.com/lKNyR.jpg)
cryptanalysis - S-AES RC[i] Generation. Can someone explain how to generate the RC[i]s for these two problems I have? - Cryptography Stack Exchange
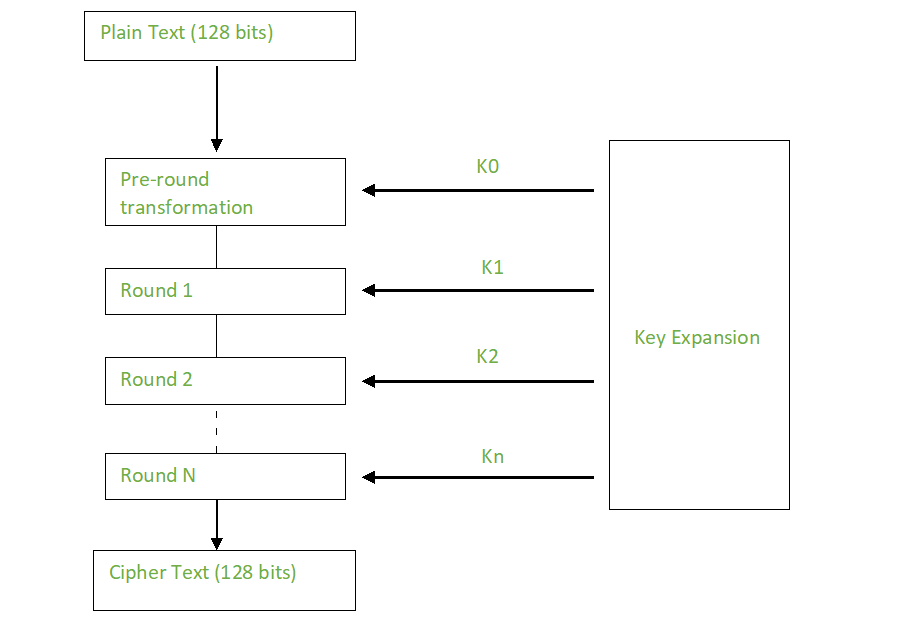
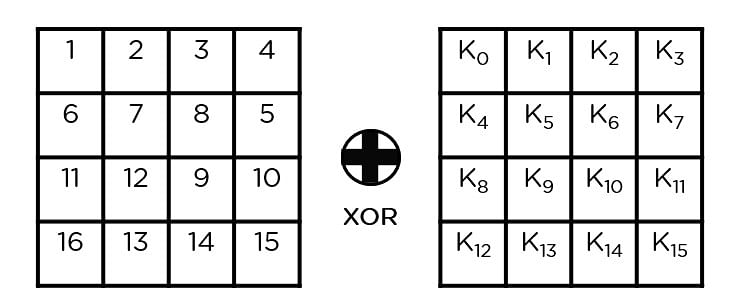
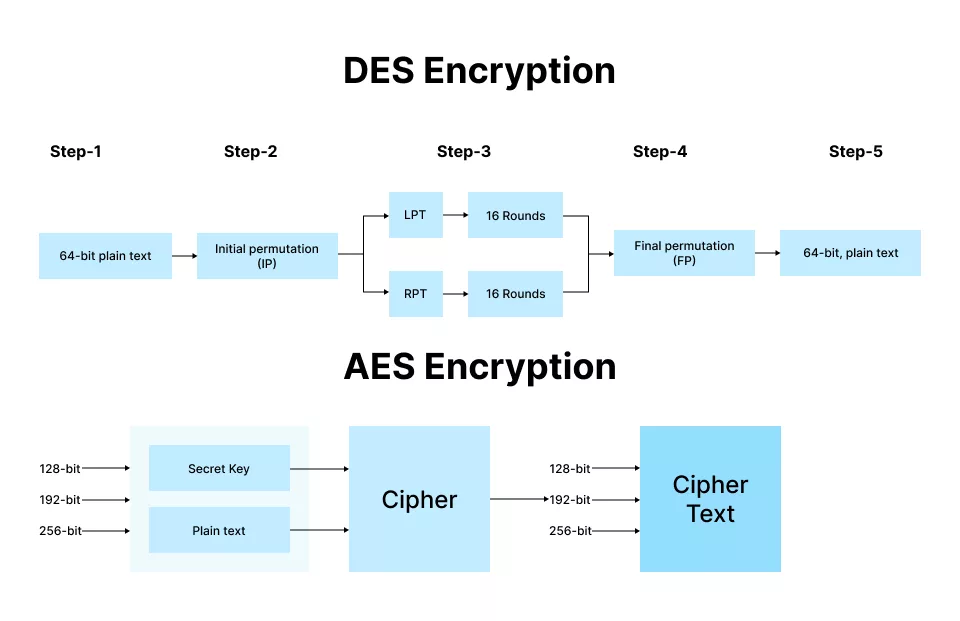
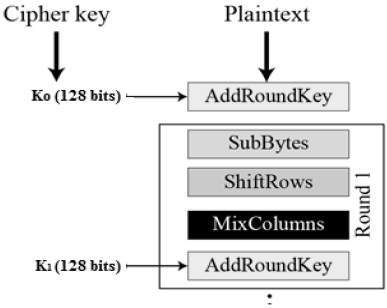
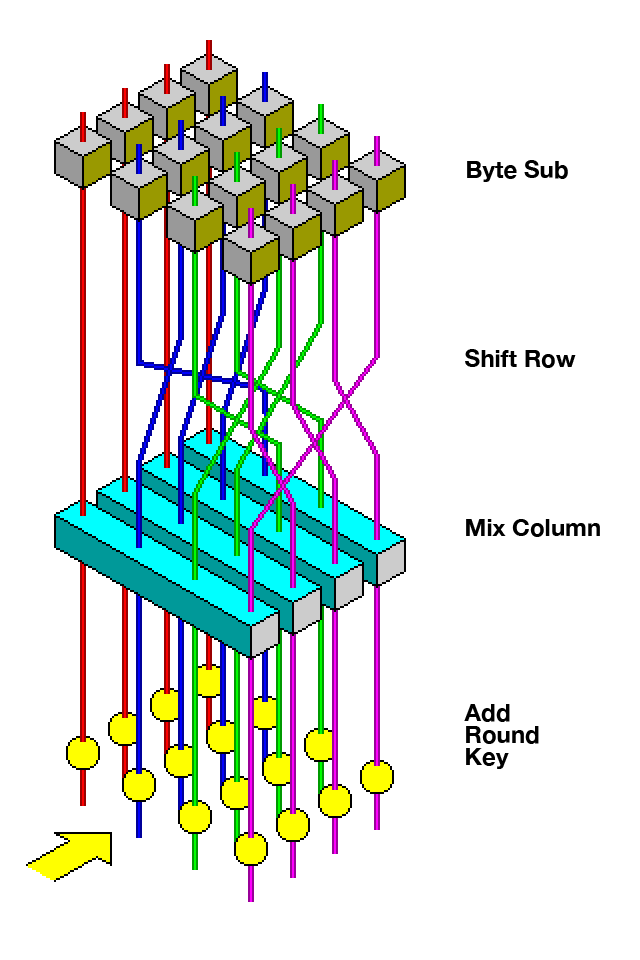
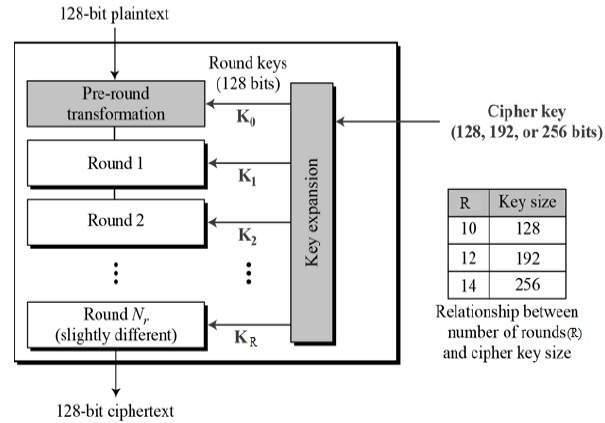
Steps in the AES Encryption Process :: Appendix A. Overview of the AES Block Cipher :: Appendixes :: 802.11 security. wi-fi protected access and 802.11i :: Networking :: eTutorials.org
![PDF] Improving Advanced Encryption Standard ( AES ) using a Novel Block Key Generation Algorithm and Dynamic S-boxes | Semantic Scholar PDF] Improving Advanced Encryption Standard ( AES ) using a Novel Block Key Generation Algorithm and Dynamic S-boxes | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/f1e8e8d996d631197d121ce19cc340a5d1033bc9/68-Figure4.16-1.png)
PDF] Improving Advanced Encryption Standard ( AES ) using a Novel Block Key Generation Algorithm and Dynamic S-boxes | Semantic Scholar

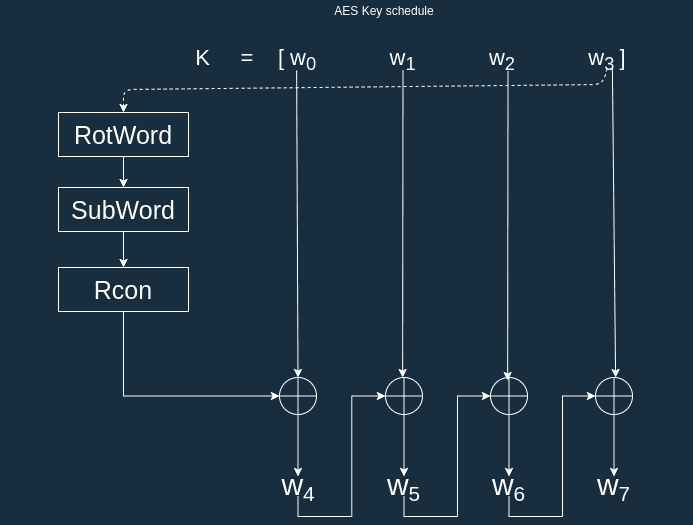
AES III - Advanced Encryption Standard - Introduction , Key Expansion in AES Cyber Security CSE4003 - YouTube
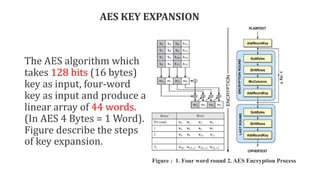
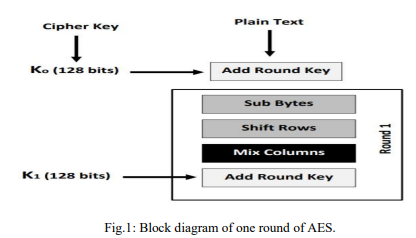
above explains the stages of the process on the encryption algorithm... | Download Scientific Diagram